3.6.2 Quiz Module 3: Industrial Cybersecurity Frameworks and Regulations Answers
3.6.2 Quiz Module 3: Industrial Cybersecurity Frameworks and Regulations Answers
The 3.6.2 Quiz Module 3: Industrial Cybersecurity Frameworks and Regulations Answers is designed to help learners review and validate their understanding of key concepts related to securing industrial control systems (ICS) and operational technology (OT) environments. This module focuses on widely recognized cybersecurity frameworks such as NIST, ISA/IEC 62443, and ISO/IEC standards, as well as important regulatory requirements that govern critical infrastructure protection. By practicing these quiz questions and answers, students can strengthen their knowledge of risk management, defense-in-depth strategies, and compliance principles essential for protecting modern industrial systems against evolving cyber threats.
1. Which statement describes the importance of adhering to Operational Technology (OT) systems regulations in critical infrastructure sectors?
- Regulatory requirements focus solely on the protection of data privacy and do not address broader security concerns in OT systems.
- Regulatory requirements for OT systems are only advisory and not enforced by any legal or governmental body.
- Regulatory requirements for OT systems are uniform across all industries and countries, simplifying compliance efforts.
- Compliance with specific regulatory requirements is crucial for maintaining secure operations in OT systems.
Adhering to regulatory requirements for Operational Technology (OT) systems is critical for organizations in critical infrastructure sectors to ensure national security, public safety, and service integrity while avoiding cyber risks and legal penalties.
2. What are the six core functions of the Cybersecurity Framework (CSF)?
- Train, Design, Identify, Detect, Recover, Govern
- Govern, Identify, Protect, Detect, Respond, Recover
- Identify, Detect, Monitor, Recover, Evaluate, Recover
- Design, Protect, Identify, Monitor, Evaluate, Respond
- Govern, Protect, Monitor, Respond, Evaluate, Recover
The six core functions of the Cybersecurity Framework (CSF) are Govern, Identify, Protect, Detect, Respond, and Recover. These functions are designed to provide a strategic view of the lifecycle of managing and mitigating cyber risk.
3. What is the consequence of failing to comply with regulatory reporting requirements in the context of cybersecurity incidents?
- hefty fines or loss of operational licenses
- public scrutiny of projects, licenses, and procedures
- removal of government subsidies for sustainable projects
- full government evaluation of company reporting procedures
Not adhering to regulatory reporting requirements can result in severe penalties, such as large fines or the loss of licenses, emphasizing the need for compliance to avoid legal and financial consequences.
4. Which statement describes the role of frameworks like NIST SP 800-82 and the NIST Cybersecurity Framework (CSF) in cybersecurity?
- They are only applicable to governmental organizations for cybersecurity risk management.
- They serve as legal documents that companies must follow under federal law.
- They offer financial assistance to companies to implement cybersecurity measures.
- They provide guidelines for managing cybersecurity risks and ensuring system compliance.
Frameworks like NIST SP 800-82 and the NIST Cybersecurity Framework (CSF) are vital in guiding organizations across various sectors in managing cybersecurity risks and ensuring best practices compliance, despite not being legally binding.
5. What is an international standard widely used in the power utility industry to ensure the efficient communication and management of automation systems within substations?
- IEC 27005
- IEC 62443
- IEC 27001
- IEC 61850-90
IEC 61850-90 is an extension of the IEC 61850 power utility automation standard, that is widely used in the power utility industry to ensure the efficient communication and management of automation systems within substations.
6. NERC is responsible for ensuring the security and reliability of the power system in what regions?
- Continental United States, Canada, Mexico, and northern Baja California
- Continental United States, Canada, and South America
- United States, Mexico, Western Europe, and Central America
- Continental United States, Canada, Eastern Europe, South America, and Australia
NERC is an international regulatory authority essential for ensuring the security and reliability of the bulk power system in North America, overseeing the continental United States, Canada, Mexico, and northern Baja California to promote unified reliability and security standards.
7. What is the scope and objective of the European Network and Information Security (NIS2) Directive?
- To ensure a unified and robust level of cybersecurity protection across all EU member states.
- To promote data privacy for consumers by regulating how personal data is processed and transferred.
- To establish a European digital currency and regulate its use across financial institutions within the EU.
- To reduce digital service taxes across the European Union and foster a competitive digital market.
The NIS2 Directive is essential EU legislation that aims to strengthen cybersecurity across member states by expanding the scope of sectors covered, enforcing stricter measures, and enhancing risk management and supply chain security against advanced cyber threats.
8. What is the purpose of the ISA/IEC 62443 series of standards, developed by the International Electrotechnical Commission (IEC)?
- international shipping and logistics standards
- development of consumer electronics interfaces
- creation of international financial reporting standards and polices
- security of Industrial Automation and Control Systems
ISA/IEC 62443, developed by the IEC, is an international series of standards designed explicitly for securing Industrial Automation and Control Systems.
9. What is the focus of the IEC 62850 series of standards?
- the interoperability of mobile devices
- the standardization of consumer electronics interfaces and communication
- the functional safety of electrical and electronic systems in machinery
- the energy efficiency in industrial processes
IEC 62850 sets safety requirements for electrical and electronic systems within machinery. This series of standards primarily addresses functional safety, aiming to protect people, equipment, and the environment from electrical hazards, particularly in industrial settings.
10. Which three statements identify the roles and responsibilities assigned to different groups involved in cybersecurity efforts for IACS, according to ISA/IEC 62443? (Choose three.)
- Component suppliers ensure their products meet specified security standards and requirements.
- Asset owners are responsible for the training and awareness programs for all staff on cybersecurity.
- Asset owners manage security policies and compliance.
- System integrators focus on secure system designs and ensuring they meet the requirements of asset owners.
- Component suppliers are responsible for secure system designs and integrating security features into products.
- System integrators are solely responsible for incident response and recovery.
- Asset owners are primarily responsible for physical security and environmental controls.
Asset owners manage security policies and compliance, ensuring that cybersecurity measures are in line with organizational goals and regulatory requirements. System integrators play a crucial role in creating secure system designs and ensuring these designs meet the specific needs of the asset owners and align with best practices in cybersecurity. Component suppliers are tasked with ensuring that their products adhere to established security standards, contributing to the overall security of the IACS.
11. Match the ISA/IEC 62443 security level to the description.
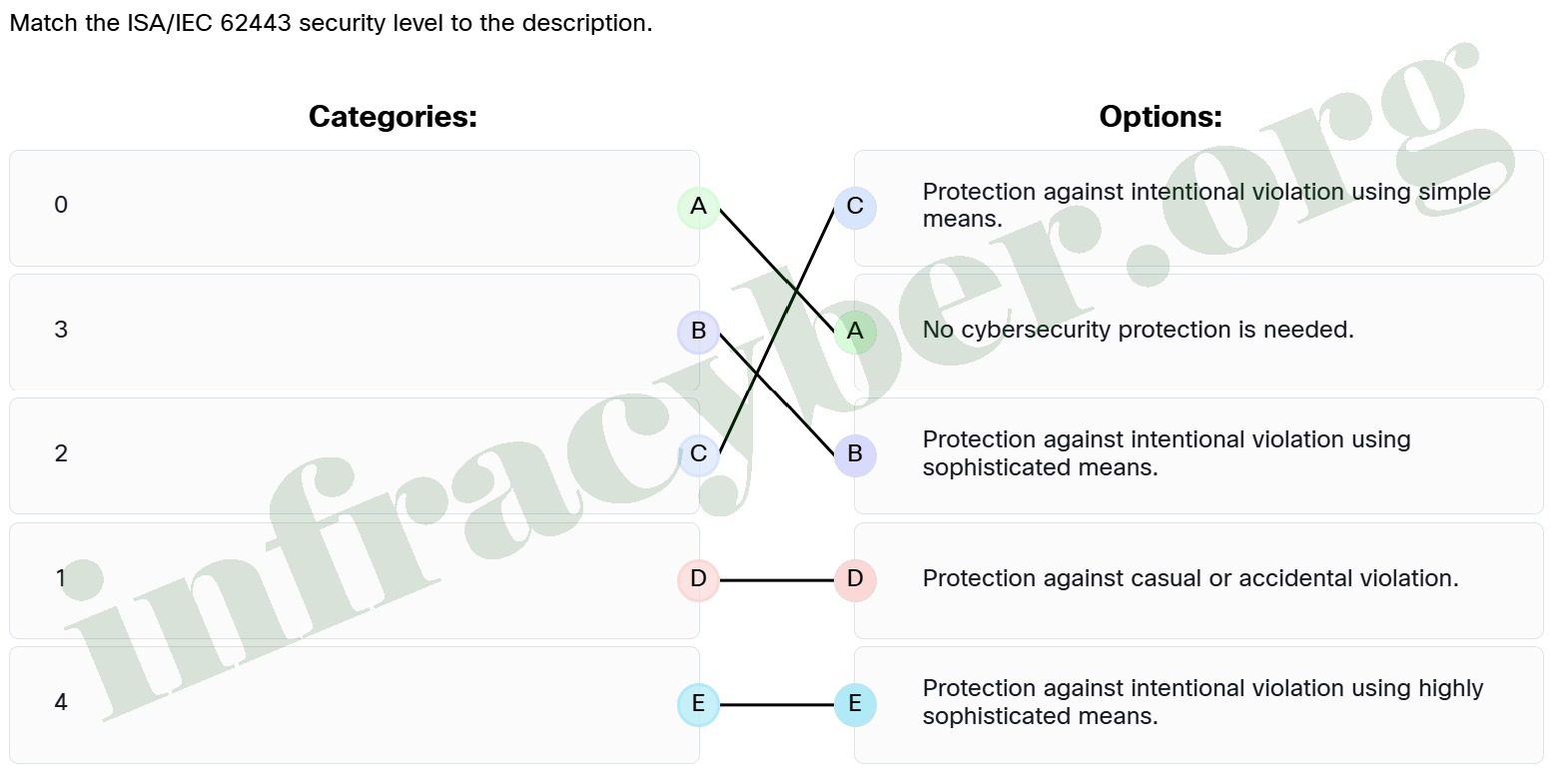
- 0 ==> No cybersecurity protection is needed.
- 1 ==> Protection against casual or accidental violation.
- 2 ==> Protection against intentional violation using simple means.
- 3 ==> Protection against intentional violation using sophisticated means.
- 4 ==> Protection against intentional violation using highly sophisticated means.
12. Which three corporations are major security providers for cybersecurity in IACS environments? (Choose three.)
- Microsoft
- Siemens
- LDRA
- Adobe
- Cisco
LDRA is recognized for its software analysis and testing products, which are crucial for ensuring security in critical systems. Siemens offers a comprehensive portfolio of security solutions, especially for industrial and infrastructure sectors, making it a major security provider. Cisco is well-known for its networking and security solutions, including firewalls, VPNs, and intrusion prevention systems.
13. What are the three key elements that form the foundation of the NIST cyber security framework? (Choose three.)
- Implementation Tiers
- User Interface
- Integration Points
- Security Measures
- Core
- Profiles
- Development Phases
The NIST Cyber Security Framework is built around three key elements: the Core, Implementation Tiers, and Profiles. The Core is the framework’s central element, providing the foundational concepts and methodologies. Implementation Tiers represent different levels of maturity and capability within the framework. Profiles allow for the customization and adaptation of the framework to specific needs or sectors.
14. What is crucial for any cybersecurity strategy to protect Operational Technology (OT) environments?
- Assuming OT systems are inherently secure and require no additional protections.
- Implementing standard office IT security protocols.
- Recognizing potential vulnerabilities specific to OT environments.
- Focusing on security solution development.
Recognizing these specific vulnerabilities allows organizations to tailor their cybersecurity measures appropriately, ensuring the safety and integrity of their critical infrastructure. Ignoring these unique aspects can expose systems to targeted attacks that exploit the distinctive nature of OT environments.
15. Which two key security standards, relevant to safeguarding IACS in industrial environments, are European Union based? (Choose two.)
- GDPR
- ISO/IEC 27001
- NERC CIP
- ISA/IEC62443
- NIST Cybersecurity Framework (CSF)
- ENISA IoT Security Guidelines
GDPR: A data privacy regulation, followed by countries in the EU and European Economic Zone (EEA), applicable to any connected system that handles personal data.
ENISA IoT Security Guidelines: Offers EU-recommended guidelines for securing IoT devices and ecosystems, with specific focus on industrial IoT.